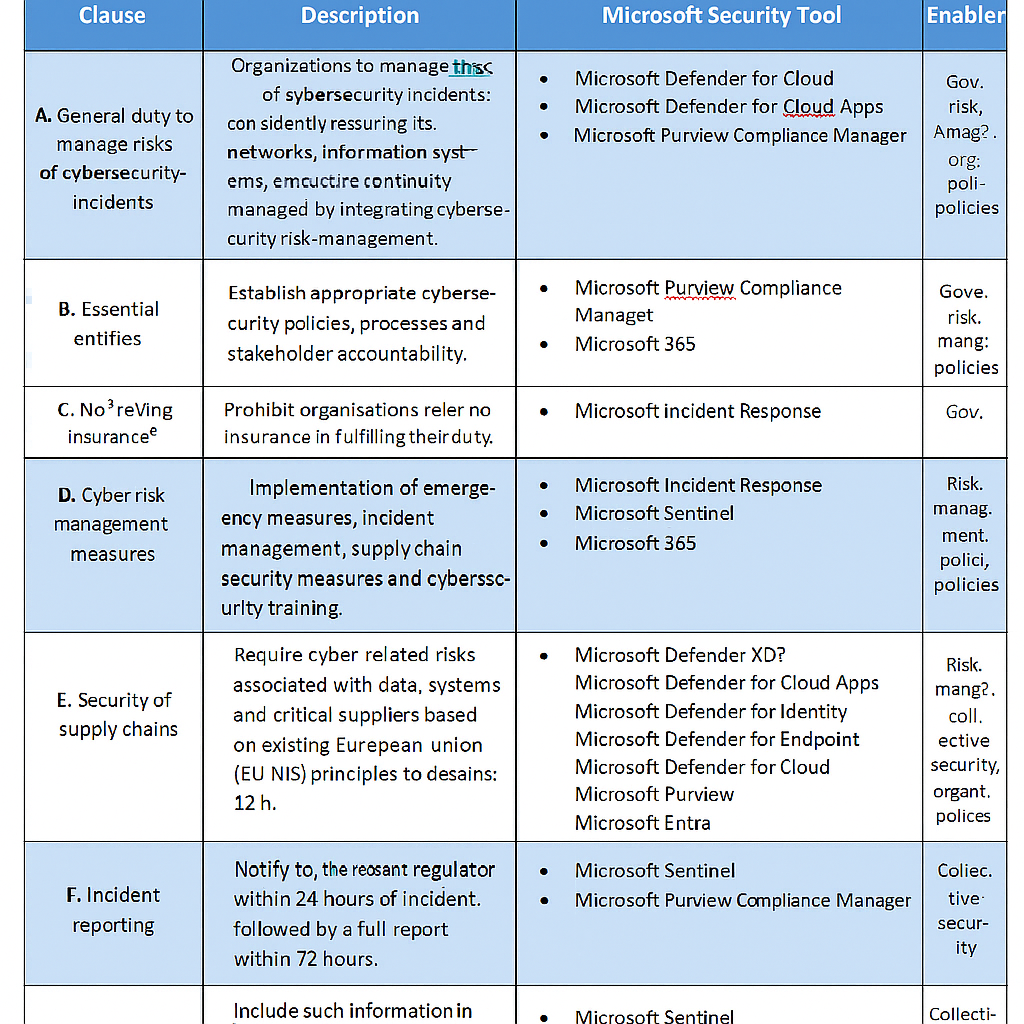
Introduction: What Is It and Why Now?
On 12 November 2025, the UK government introduced the Cyber Security and Resilience (Network and Information Systems) Bill to Parliament. It’s being hailed as the most significant overhaul of UK cyber law since the NIS Regulations of 2018. The aim? To stop the lights going out, the taps running dry, and the NHS from being held hostage by ransomware gangs with more imagination than morals.
The Bill updates the old NIS framework and borrows heavily from the EU’s NIS2 Directive, but with a distinctly British twist: more scope, tougher penalties, and emergency powers for ministers. If passed (Royal Assent expected in 2026), compliance will be mandatory for thousands of organisations, including operators of essential services, managed service providers (MSPs), data centres, and designated “critical suppliers” in the supply chain. Failure to comply could mean turnover-based fines that make GDPR look like a parking ticket.
The Positives: Why It’s a Step Forward
Broader Scope
The Bill finally recognises that attackers don’t politely knock on the front door—they stroll in through the supplier entrance. By regulating MSPs, data centres, and critical suppliers, the law closes glaring gaps in the UK’s digital ecosystem.
Microsoft’s role: Tools like Microsoft Defender for Cloud and Microsoft Sentinel provide continuous monitoring across hybrid supply chains, helping organisations identify risks in third-party integrations and cloud workloads before attackers exploit them.
Mandatory Incident Reporting
Organisations must report significant cyber incidents within 24 hours, followed by a full report in 72 hours. This should end the “bury it and hope no one notices” approach that some firms have favoured.
Microsoft’s role: Microsoft Sentinel offers automated incident detection, correlation, and reporting dashboards. Combined with Microsoft Purview Compliance Manager, firms can generate regulator-ready reports quickly, reducing the risk of missing deadlines.
Alignment with Best Practice
Compliance will be tied to the NCSC Cyber Assessment Framework (CAF), ensuring a consistent, risk-based approach rather than a tick-box exercise.
Microsoft’s role: The Microsoft Security Compliance Toolkit and Purview Risk & Compliance solutions map directly to CAF principles, enabling organisations to benchmark their controls against UK standards and demonstrate alignment with best practice.
Serious Enforcement
Turnover-based penalties mean that cutting corners is no longer cheaper than doing the right thing. For large firms, this could be the nudge they need to invest before—not after—a breach.
Microsoft’s role: Defender for Endpoint and Defender for Identity reduce breach likelihood by hardening endpoints and identities. Investment in these tools is cheaper than fines and reputational damage.
Emergency Powers
Ministers can direct regulators and organisations during live incidents. In theory, this means action in minutes rather than weeks. In practice, let’s hope it doesn’t involve a committee meeting first.
Microsoft’s role: With Microsoft Incident Response services and Sentinel playbooks, organisations can execute rapid, automated containment actions—exactly the kind of agility regulators will expect under emergency powers.
The Negatives: Why It’s Raising Eyebrows
- Compliance Burden – For MSPs and mid-sized firms, the cost and complexity of meeting these standards could be significant. Many will need to overhaul processes, invest in SOC maturity, and renegotiate contracts.
- Microsoft’s stack helps reduce cost by offering integrated security across identity, endpoint, cloud, and compliance—avoiding the “patchwork quilt” of multiple vendors.
- Ambiguity in Enforcement – While penalties are clear, some details—such as what qualifies as a “significant” incident—remain fuzzy.
- Microsoft Sentinel’s analytics can help categorise incidents consistently, providing defensible evidence if enforcement disputes arise.
- Rapid Legal Change – Obligations can be updated via secondary legislation. Flexibility is good, but constant change could leave businesses chasing a moving target.
- Microsoft Purview’s compliance score updates dynamically with regulatory changes, helping organisations keep pace without reinventing the wheel.
- Supply Chain Complexity – Designating “critical suppliers” sounds sensible until you realise how sprawling supply chains are.
- Microsoft Defender for Cloud Apps provides visibility into shadow IT and supplier integrations, helping firms identify which suppliers are truly “critical.”
What It Means for MSPs Like Creative
For MSPs, this Bill is a wake-up call—though some have been awake for years..They’ve been preaching Third-Party Risk Management (TPRM) to their clients long before it was fashionable, anticipating exactly this kind of regulation.
Some even offer a dedicated TPRM-as-a-Service function, monitoring its client’s critical suppliers 24/7 across:
- External security posture
- Dark web mentions
- Responsiveness ratings for vulnerability remediation
In short, they’ve built resilience into their DNA, not just their marketing. For MSPs that haven’t, now’s the time to start—because under this Bill, ignorance won’t just be expensive, it’ll be illegal.
Microsoft’s role for MSPs: By leveraging Microsoft Entra ID (Azure AD) for secure identity management, Defender for Cloud for supplier posture monitoring, and Sentinel for SOC maturity, MSPs can operationalise compliance without reinventing their service model.
A Note on Cyber Essentials: The Power of Simplicity
Before we drown in regulatory complexity, let’s remember Cyber Essentials—the UK’s humble five-control scheme. Research shows it can mitigate 99% of internet-originating vulnerabilities and has slashed cyber insurance claims by 75–92%, depending on the study. All with basic measures like patching, access control, and malware protection. Proof that sometimes, the simplest things work best—rather like locking your front door before installing a biometric retina scanner.
Microsoft’s role: Cyber Essentials controls map neatly to Microsoft’s baseline security:
- Patch management → Windows Update & Intune
- Access control → Entra ID with Conditional Access
- Malware protection → Defender Antivirus & Defender for Endpoint
- Secure configuration → Intune compliance policies
- Firewall & network security → Azure Firewall and Defender for Cloud
Final Thoughts
The Cyber Security and Resilience Bill is ambitious, necessary, and overdue. It promises a safer digital Britain, but at the cost of more paperwork, higher compliance budgets, and a few headaches for supply chain managers. Still, given that cyberattacks cost the UK economy £14.7 billion a year, it’s hard to argue against stronger measures.
Whether this Bill becomes a triumph or a bureaucratic quagmire will depend on how clearly it’s implemented and whether organisations embrace the spirit of resilience rather than just the letter of the law.
In the meantime, if you haven’t got Cyber Essentials yet, do yourself a favour: start there. And if you want to go further, the Microsoft security stack offers a ready-made toolkit to meet compliance, reduce risk, and prove resilience—before regulators come knocking.